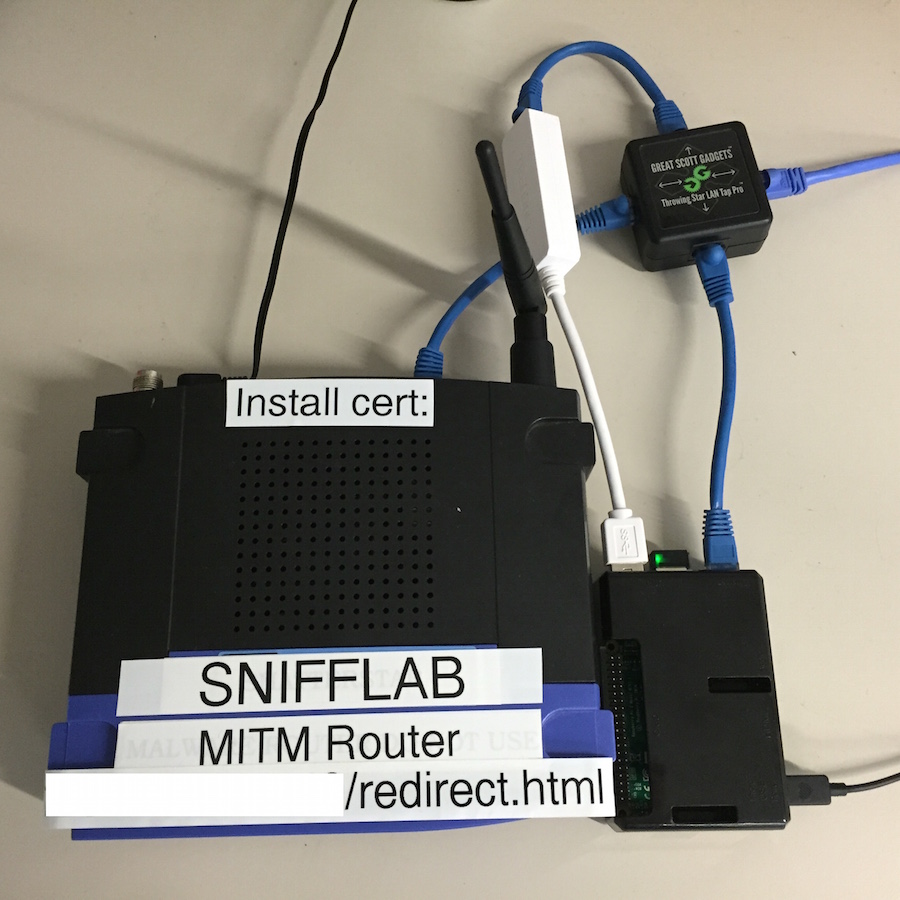
TAP is a remote penetration testing platform builder. For folks in the security industry, traveling often times becomes a burden and adds a ton of cost to...

Jok3r is a Python3 CLI application which is aimed at helping penetration testers for network infrastructure and web black-box security...

Sh00t is a task manager to let you focus on performing security testing provides To Do checklists of test cases helps to create bug reports with...

As the name might suggest AutoSploit attempts to automate the exploitation of remote hosts. Targets are collected automatically as well by employing the...
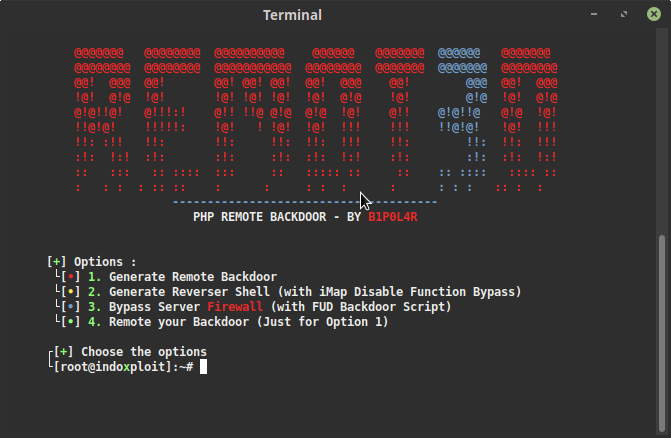
It's easy to create a backdoor in an instant, the backdoor can be used in a remote process via a Linux terminal on the server that runs the PHP Language...

"PRinter Exploitation Toolkit" LAN automation tool PRETty is useful when a large number of printers are present on a network. Instead of scanning, logging,...

An RTSP stream access tool that comes with its library Docker Image for Cameradar Install docker on your machine, and run the following...

Sn1per Community Edition is an automated scanner that can be used during a penetration test to enumerate and scan for vulnerabilities....

Initial attack vectors for recon usually involve utilizing pay-for-data/API (Recon-NG), or paying to utilize transforms (Maltego) to get data...

Hardware: Spoof Device ID, Vendor Id/ Fake Device ID, Vendor Id Spoof BIOS manufacturer, version, date etc./ Fake BIOS manufacturer, version, date...

Deep Exploit at Black Hat USA 2018 Arsenal. DeepExploit is fully automated penetration test tool linked with Metasploit.It has two...

SleuthQL is a python3 script to identify parameters and values that contain SQL-like syntax. Once identified, SleuthQL will then insert SQLMap identifiers...

msploitego leverages the data gathered in a Metasploit database by enumerating and creating specific entities for services. Services like samba,...

Auto exploiter & get all server sites & bing dorker. Version 2.0 Fixed colors bug Fixed permissions bug Added new option to scan single...

Gpredict is a real-time satellite tracking and orbit prediction application. It can track a large number of satellites and display their position and other...

This tool will setting up your backdoor/rootkits when backdoor already setup it will be hidden your spesisifc process,unlimited your session in metasploit...

The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for...

Sn1per is an automated scanner that can be used during a penetration test to enumerate and scan for vulnerabilities. FEATURES: Automatically...

The macro_pack is a tool used to automatize obfuscation and generation of retro formats such as MS Office documents or VBS like format. This tool can be...

Autorize is an automatic authorization enforcement detection extension for Burp Suite. It was written in Python by Barak Tawily, an application security...

Simple TCP reverse shell written in Go. It uses TLS to secure the communications, and provide a certificate public key fingerprintpinning feature,...

OnionHarvester - A small TOR Onion Address harvester for checking if the address is available or not
A small TOR Onion Address harvester for checking if the address is available or not. The program uses the TOR local socks5 proxy for finding all...
X Attacker Tool ☣ Website Vulnerability Scanner & Auto ExploiterYou can use this tool on your website to check the security of your website by finding the...

Features: High speed and precision CLI ( Console based ) Run the arbitrary command after the attack is successful ( Default 'Uname -a' ) Telegram messanger...
Sublist3r is a python tool designed to enumerate subdomains of websites using OSINT. It helps penetration testers and bug hunters collect and gather...
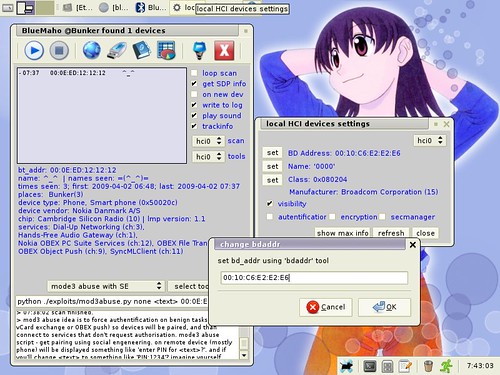
BlueMaho is GUI-shell (interface) for suite of tools for testing security of bluetooth devices. It is freeware, opensource, written on python, uses wxPyhon....

Archery is an opensource vulnerability assessment and management tool which helps developers and pentesters to perform scans and manage vulnerabilities....

(s)AINT is a Spyware Generator for Windows systems written in Java. Features Keylogger Take Screenshot Webcam Capture Persistence Tested...

WSC2 is a PoC of using the WebSockets and a browser process to serve as a C2 communication channel between an agent, running on the target system, and a...

Excalibur is an Eternalblue exploit based "Powershell" for the Bashbunny project. It's purpose is to reflect on how a "simple" USB drive can execute the 7...

SpookFlare has a different perspective to bypass security measures and it gives you the opportunity to bypass the endpoint countermeasures at the...

Enigma is a Multiplatform payload dropper. Run git clone https://github.com/UndeadSec/Enigma.git cd Enigma python enigma.py or python3...

DumpsterFire Toolset - "Security Incidents In A Box!" The DumpsterFire Toolset is a modular, menu-driven, cross-platform tool for building repeatable,...

A CMS Exploit Framework. Requirements python2.7 Works on Linux, Windows Usage usage: cmspoc.py [-h] -t TYPE -s SCRIPT -u URL optional arguments: ...

Mentalist is a graphical tool for custom wordlist generation. It utilizes common human paradigms for constructing passwords and can...

Ethereum wallet recovery password multithread tool, baked from pyethrecover and pyethereum, for using keystore v3 json file to help...

Shellsploit let’s you generate customized shellcodes, backdoors, injectors for various operating system. And let’s you obfuscation every byte via...
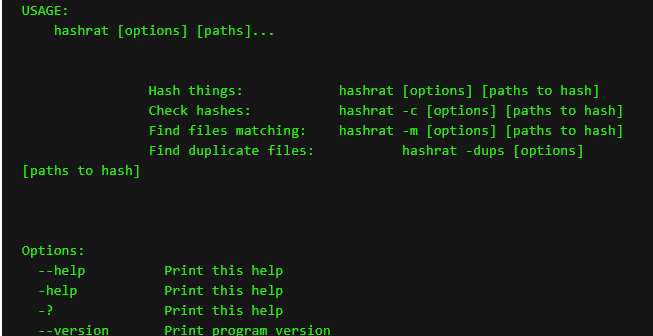
Hashrat is a command-line utility that hashes things using md5, sha1/256/512, whirlpool and jh hash algorithms. It's written in C with few dependancies...

Usage usage: cmspoc.py [-h] -t TYPE -s SCRIPT -u URL optional arguments: -h, --help show this help message and exit -t TYPE, --type TYPE ...
![Crawler File [No WebCrawler] [Local File Crawler]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEh1w2sNFTGfhXsgbbAVaJx4_Nik3azS2VYf8pgngTrrjqWhDlzoNL3UtWAeA74y9Mweit-UXCjcm00slARlFhZ_IYY_-F84ahExxxpVoZFFILLHXzGbYo8Q-EdDpoHg1sWWWYa6UQurR8sM/s1600/fatcrawler.PNG)
-d –dir The start directory path (required) -t –file-type The file type to lookup (required) -c –chunk-size The chunk size to report to the...

Features Easy target selections Smart form and error detection CSRF and Clickjacking Scanner Cloudflare and WAF Detector 90% accurate results Checks for...

Easily launch a new phishing site fully presented with SSL and capture credentials along with 2FA tokens using CredSniper. The API...

TrevorC2 is a client/server model for masking command and control through a normally browsable website. Detection becomes much harder as time intervals are...

Use nmap to scan hidden "onion" services on the Tor network. Minimal image based on alpine, using proxychains to wrap nmap. Tor and dnsmasq...

Paskto will passively scan the web using the Common Crawl internet index either by downloading the indexes on request or parsing data from your local...

An unicode domain phishing generator for IDN Homograph Attack. VIDEO DEMO CLONE git clone...

What Droidefense is? Droidefense (originally named atom: analysis through observation machine)* is the codename for android apps/malware...
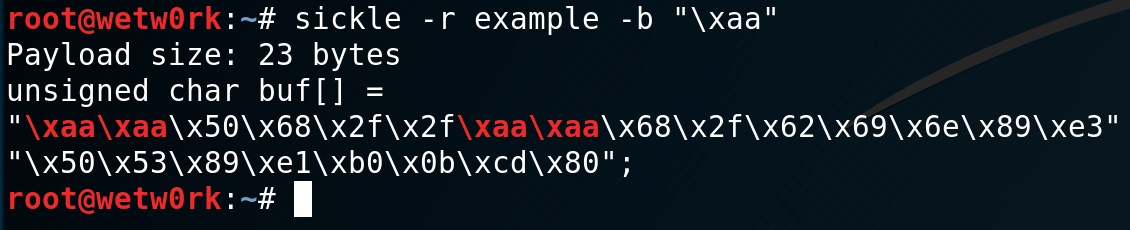
Sickle is a shellcode development tool, created to speed up the various steps needed to create functioning shellcode. Sickle can aid in the following: –...