
What is phishing kit?Phishing kits are generally kits provided by cyber-criminals to allow anyone with a little bit of IT knowledge to carry out a phishing...

It might take a while until further things will be released, while my source makes sure they're safe. If you find password protected zips in the...

Security researchers discovered a new vulnerability in WPA3 Protocol named as “Dragonblood” allows hackers to steal the WiFi Password from WP3 enabled...

Google play Store flooding the several malicious beauty camera apps that steal Android users sensitive images and apps, the malicious app was already...

Totally 87GB data – Find out if you are affected by the massive data breach. Security researcher and founder of Have I Been Pwned, Troy Hunt, has...

In 2015 two hackers managed to hack TalkTalk, a major UK based telecoms company, stealing information of more than 156,000 customers. This...

Earlier this week Dropbox team unveiled details of three critical vulnerabilities in Apple macOSoperating system, which altogether could allow a remote...

Looking for a hack to bypass the passcode or screen lock on iPhones? Jose Rodriguez, an iPhone enthusiast, has discovered a passcode bypass vulnerability...

A security researcher has publicly disclosed the details of a previously unknown zero-day vulnerability in the Microsoft's Windows operating system that...

A group Kurdish hacker group hacked a Turkish municipality and sent an SMS in its name commemorating a violent act perpetrated by the Kurdistan Workers’...

Refuting allegations that its anti-virus product helped Russian spies steal classified files from an NSA employee's laptop, Kaspersky Lab has...

Just a week after Apple released its brand new iPhone X on November 3, a team of hackers has claimed to successfully hack Apple's Face ID facial recognition...

Almost two months after releasing details of 23 different secret CIA hacking tool projects under Vault 7 series, Wikileaks today...

Horrible news for some Ethereum users. About $300 million worth of Ether—the cryptocurrency unit that has become one of the most popular and increasingly...

Within a few cycles, researchers displayed the system in the lab, and today quantum cryptography is displaying commercially viable recognition to companies...

Another day, Another data breach disclosure.This time the popular commenting system has fallen victim to a massive security breach.Disqus, the company...

A group affiliated with the online activist group known as Anonymous 17 August posted what it says are the private cellphone numbers and email addresses for...

A massive archive of Microsoft's top-secret Windows 10 builds, and the source codes for private software has been reportedly leaked online, which could lead...

South Korean web hosting provider has agreed to pay $1 million in bitcoins to hackers after a Linux ransomware infected its 153 servers, encrypting 3,400...

The whistleblowing site WikiLeaks is back with yet another Vault 7 series related document. This one is called “Cherry Blossom” program which gives a glance...

Authorities have conducted a large-scale operation against cyber criminals in several European countries. As a result, 6 people have been arrested while 36...

It’s been almost four weeks since the outcry of WannaCry ransomware, but the hackers behind the self-spread ransomware threat have not been identified...

CVE : https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7494 The seven-year-old exploit, indexed as CVE-2017-7494, are often reliably exploited with...
Researchers have detected a new worm that is spreading via SMB, but unlike the worm component of the WannaCry ransomware, this one is using seven NSA tools...
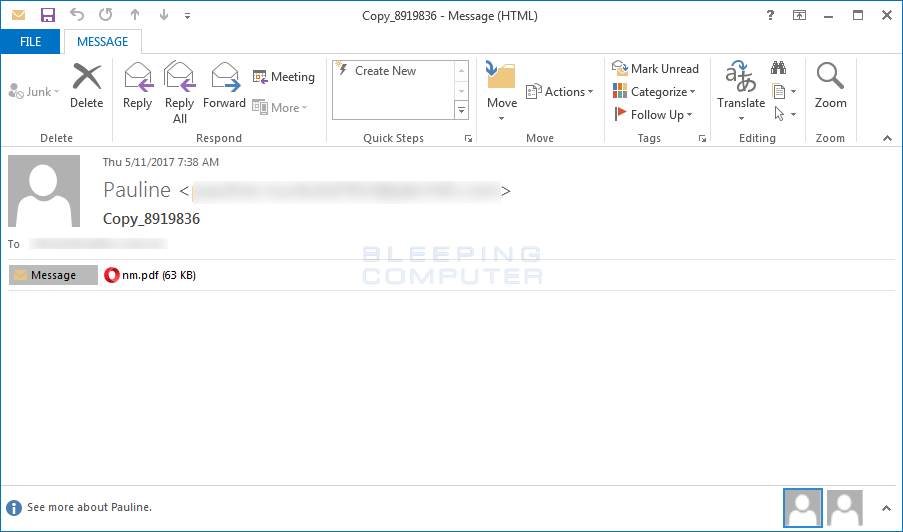
A new ransomware was found today by Malwarebytes' malware researcher S!Ri called Jaff Ransomware. In general, there is nothing special about...

A security researcher has discovered a serious vulnerability in the default configuration of the latest version of Google's Chrome running on any version of...

A group of hackers that previously leaked alleged U.S. National Security Agency exploits claims to have even more attack tools in its possession and...

Hey, Hope all of you already get knew about WannaCry Ransomware which has already hit more than 200000 computers. And don’t think that it’s over, here...

Update — We have published another article with more detailed information on the WannaCry ransomware attack that has become the...

Wikileaks has just published a new batch of the Vault 7 leak, exposing the documentation and source code for a CIA project known as...

Many people believe that they are much less likely to be bothered by malware if they use a Mac computer, but is it really true? Unfortunately,...

Last week, we reported about a so-called 'vigilante hacker' who hacked into at least 10,000 vulnerable 'Internet of Things' devices, such as home...

Initially thought to be 600,000 users, the number of Android users who have mistakenly downloaded and installed malware on their devices straight from...

Atlassian's group chat platform HipChat is notifying its users of a data breach after some unknown hacker or group of hackers broke into one of its servers...

Script kiddies and online criminals around the world have reportedly started exploiting NSA hacking tools leaked last weekend to compromise...

Bad news for consumers with Linksys routers: Cybersecurity researchers have disclosed the existence of nearly a dozen of unpatched security flaws in...

The tools were dumped via the Shadow Brokers Twitter account and were accompanied by a blog post, as the group did in the past. Called "Lost in...

The latest dump of hacking tools allegedly belonged to the NSA is believed to be the most damaging release by the Shadow Brokers till the...

A Russian computer hacker arrested over the weekend in Barcelona was apparently detained for his role in a massive computer botnet, and not for last year's...

Security researchers have confirmed that the alleged CIA hacking tools recently exposed by WikiLeaks have been used against at least 40 governments and...

We have seen hackers flooding 911 emergency service with rogue requests to knock the service offline for an entire state, but some hacking incidents are...

A Russian computer hacker and alleged spam kingpin was arrested in Barcelona, Spain, on Friday reportedly over suspicion of being involved in hacking...

It's 2017, and opening a simple MS Word file could compromise your system.Security researchers are warning of a new in-the-wild attack that silently...

The Shadow Brokers is the mysterious group that in October 2016 claimed to have stolen a bunch of hacking tools used by the NSA for its...
March 31st 2017, WikiLeaks releases Vault 7 "Marble" -- 676 source code files for the CIA's secret anti-forensic Marble Framework. Marble is used to hamper...
