BitCracker - Bitlocker password cracker
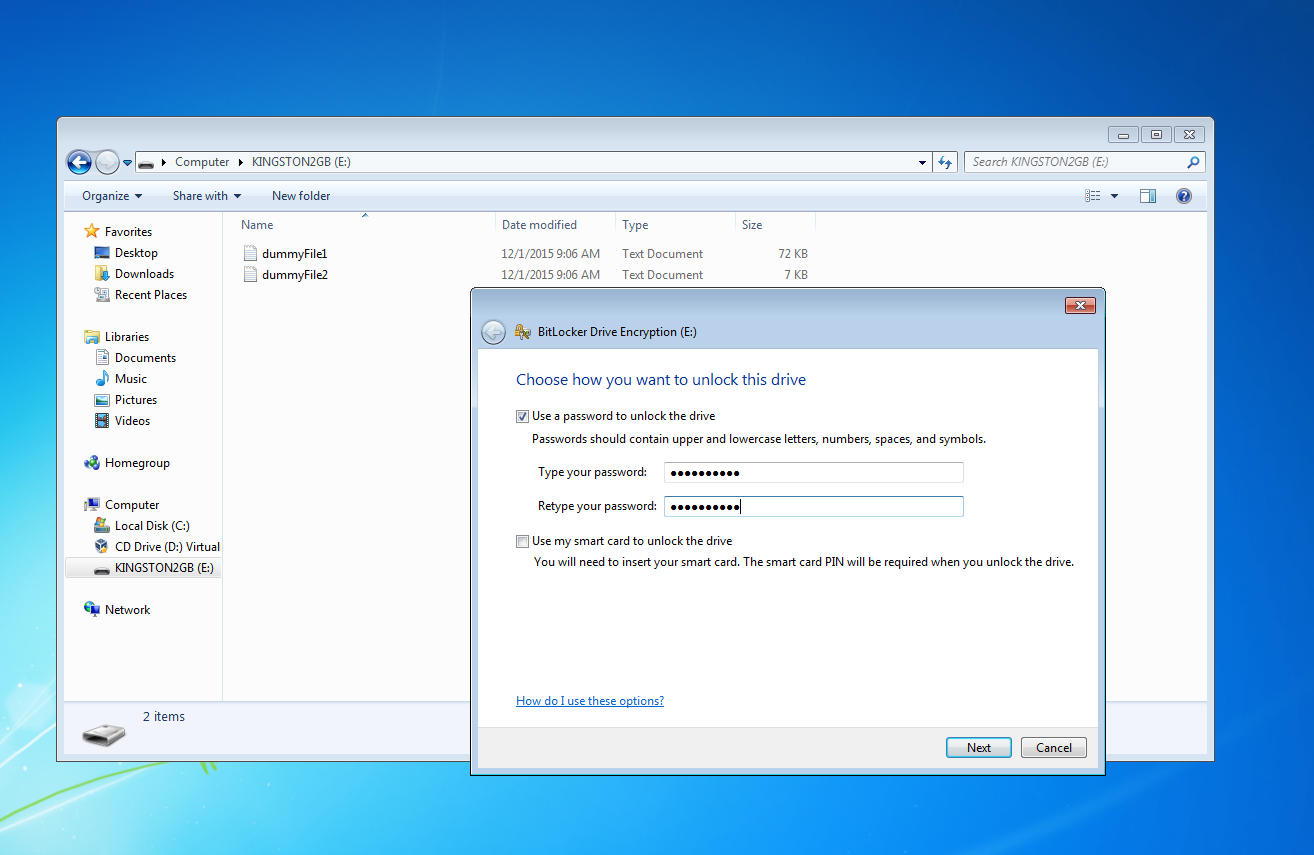
BitLocker is a full-disk encryption feature available in recent Windows versions (Vista, 7, 8.1 and 10) Pro and Enterprise. BitCracker is a mono-GPU password cracking tool for memory units encrypted with the password authentication mode of BitLocker (see picture below).
Our attack has been tested on several memory units encrypted with BitLocker running on Windows 7, Window 8.1 and Windows 10 (both compatible and non-compatible mode). Here we present two implementations: CUDA and OpenCL.
Requirements
For CUDA implementation, you need at least CUDA 7.5 and an NVIDIA GPU with minimum cc3.5 (i.e. Kepler arch)
How To
Use the build.sh script to build 3 executables:
- hash extractor
- BitCracker CUDA version
- BitCracker OpenCL version
The executables are stored in the build directory.
Before starting the attack, you need to run bitcracker_hash to extract the hash from the encrypted memory unit.
Before starting the attack, you need to run bitcracker_hash to extract the hash from the encrypted memory unit.
> ./build/bitcracker_hash -h Usage: ./build/bitcracker_hash -i <Encrypted memory unit> -o <output file> Options: -h, --help Show this help -i, --image Path of memory unit encrypted with BitLocker -o, --outfile Output file
The extracted hash is fully compatible with the John The Ripper format (see next Section).
Then you can use the output hash file to run the BitCracker attack.
> ./build/bitcracker_cuda -h Usage: ./build/bitcracker_cuda -f <hash_file> -d <dictionary_file> Options: -h, --help Show this help -f, --hashfile Path to your input hash file (HashExtractor output) -s, --strict Strict check (use only in case of false positives) -d, --dictionary Path to dictionary or alphabet file -g, --gpu GPU device number -t, --passthread Set the number of password per thread threads -b, --blocks Set the number of blocks
N.B. In case of false positives, you can use the -s option (strict check empirically verified, it works with this repo images encrypted with Windows 7, 8.1 and 10).
In the the run_test.sh script there are several attack examples using the encrypted images provided in this repo:
- imgWin7: memory unit encrypted with BitLocker using Windows 7 Enteprise edition OS
- imgWin8: memory unit encrypted with BitLocker using Windows 8 Enteprise edition OS
- imgWin10Compatible.vhd: memory unit encrypted with BitLocker (compatible mode) using Windows 10 Enteprise edition OS,
- imgWin10NonCompatible.vhd: memory unit encrypted with BitLocker (NON compatible mode) using Windows 10 Enteprise edition OS,
- imgWin10CompatibleLong27.vhd: memory unit encrypted with BitLocker (compatible mode) using Windows 10 Enteprise edition OS using the longest possible password (27 characters)
Currently, BitCracker is able to evaluate passwords having length between 8 (minimum password length) and 27 characters (implementation reasons).
BitCracker doesn't provide any mask attack, cache mechanism or smart dictionary creation; therefore you need to provide your own input dictionary.



Post a Comment